AI-driven cyberattacks are becoming increasingly more common as AI technology advances. IBM uses AI to accelerate cybersecurity defenses, while cybercriminals exploit it for malicious purposes. Attacks such as automated spear-phishing, deepfake impersonation, and AI-enhanced credential stuffing are growing threats. This article explores how cybercriminals leverage AI, ways to mitigate and detect these attacks, and how to respond effectively if targeted.




How Cybercriminals Are Using AI
Automated spear-phishing: Spear-phishing is when attackers send high-quality and legitimate-looking messages to a very specific person or group. Attacks like these take a lot of time since they must craft quality messages and find a list of potential targets. Attackers integrate AI to automate the creation of these messages, with enough examples, the AI can generate messages that an expert attacker would make. AI can also be used to scrub through records to identify potential victims based on criteria such as specific companies and specific roles they are in. Deepfake impersonation: Deepfakes use AI to create realistic video or audio impersonation of individuals by analyzing thousands of images of voice samples. Attackers can combine deepfake technology with voice cloning to make a very believable impersonation of someone a victim may know. Just 4 years ago, a bank manager received a call from his director to transfer $35 million to make an acquisition, in reality, the director was a voice clone and just a cybercriminal in disguise. AI-enhanced credential stuffing: Credential stuffing is when cybercriminals use stolen account details to gain access to private accounts. Attackers use AI to scan through public documents or data breaches to get as much information as possible in seconds. Then they will automate the process of testing combinations of usernames and passwords to infiltrate accounts effectively.
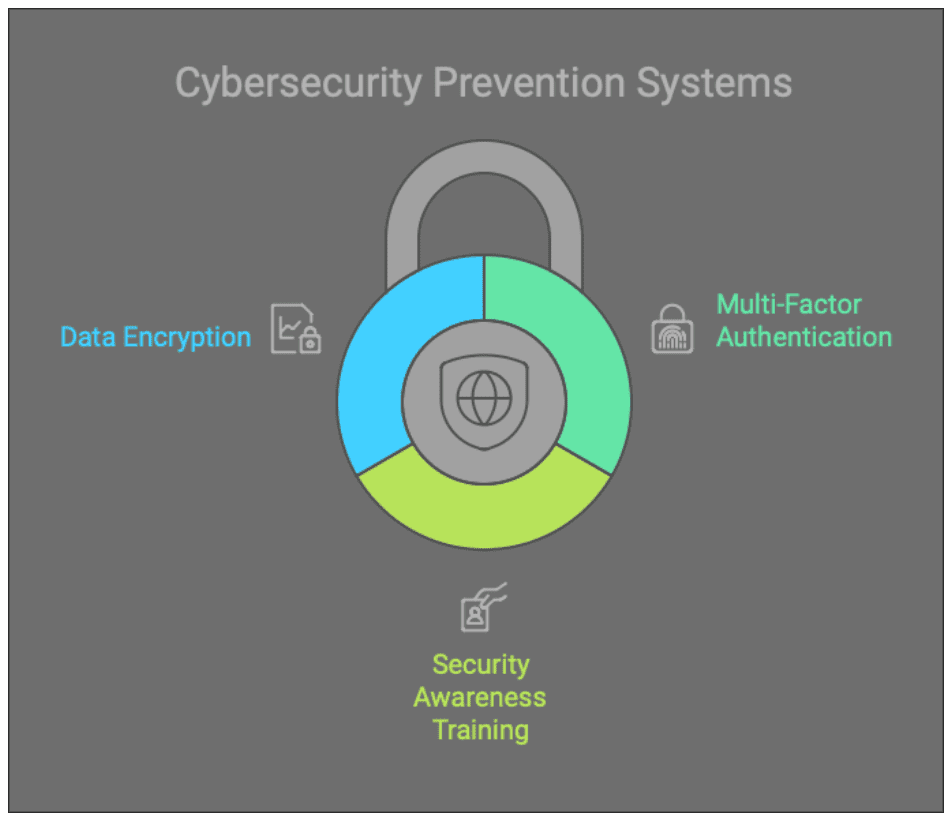
Ways to Mitigate AI-Driven Cyberattacks
The best defense against AI-driven cyberattacks is a proactive, multi-layered approach. Key strategies include:- Multi-Factor Authentication (MFA): Using just one password isn’t enough nowadays. Implementing multiple authentications to get into your accounts is crucial in this evolving Internet of Things (IoT) landscape. Fingerprint scanning, security questions, one-time password tokens, or authentication apps can significantly reduce the risk of credential stuffing or other AI-driven cyberattacks.
- Security awareness training: Training employees on cybersecurity best practices is essential. Training programs teach staff how to identify these AI-driven cyberattacks and how to respond appropriately. Regular training ensures employees remain vigilant against evolving threats.
- Data encryption: Encryption scrambles data into unreadable formats that can only be decrypted through a key. Encrypting sensitive information enhances privacy and protects against data breaches, even if attacks gain unauthorized access.
How to detect AI Cyberattacks
Early detection is vital to minimize the impact of a cyberattack. Here are some key detection methods:- Endpoint Detection and Response (EDR): EDR software monitors devices and networks to look for suspicious activity. Endpoints such as laptops or phones are common entry points for cybercriminals. That’s why we at Kirkham IronTech use EDR to reduce the risk of security breaches, improve threat intelligence, and create a streamlined security plan.
- Active monitoring: Active monitoring is another layer of protection that we offer at Kirkham IronTech. This ensures any security incidents are detected and addressed in a timely manner. Doing so greatly reduces the risk of a data breach or other cyberattack.
- Email detection: Another way we can detect potential AI cyberattacks is through our email detection systems. Our tools flag suspicious emails, move them to junk folders, and provide our clients with guidance on how to handle them. Doing so helps prevent automated spear-phishing attacks and ensures our clients avoid falling victim to attackers.
Responding to AI Cyberattacks
If cybersecurity defenses are breached, a rapid and effective response is crucial. Here’s how Kirkham IronTech can assist you: Incident Response- Our team provides fast incident response services, including malware removal, data recovery, and containment of compromised systems. By isolating affected areas and conducting analysis, we minimize damage and secure your environment.
- We design tailored security strategies for each client to address their unique needs. This may include conducting audits, annual risk assessments, and implementing advanced tools such as cloud security to encompass a wide range of systems.
- We offer free cybersecurity assessments to help businesses evaluate their current defenses. From vulnerability assessments to disaster recovery planning, our solutions ensure a long-term defense against any AI-driven cyber threats. Come schedule an appointment with us today to see how we can help you or your business.

 Tom Kirkham brings more than three decades of software design, network administration, and cybersecurity knowledge to organizations around the country. During his career, Tom has received multiple software design awards and founded other acclaimed technology businesses.
Tom Kirkham brings more than three decades of software design, network administration, and cybersecurity knowledge to organizations around the country. During his career, Tom has received multiple software design awards and founded other acclaimed technology businesses.
